 One of our class discussions this week was about communicating technical terms to non-technical audiences. The best way to present technical terms to nontechnical people is by relating it to terms that they are familiar with in their daily lives. People are more likely to understand technical terms with explanations related to activities or items they interact with on a regular basis. Let’s look at digital forensic artifacts and file signature explanations as examples.
One of our class discussions this week was about communicating technical terms to non-technical audiences. The best way to present technical terms to nontechnical people is by relating it to terms that they are familiar with in their daily lives. People are more likely to understand technical terms with explanations related to activities or items they interact with on a regular basis. Let’s look at digital forensic artifacts and file signature explanations as examples.
Digital forensic artifacts – Technical:
Binary values, or bits, that are left over after any application, file, or process is used on a computer (Mabuto and Venter, 2013).
Digital forensic artifacts – Nontechnical:
Think of credit card spending over the holidays. You may go to 20 different stores to purchase gifts for family, friends, and loved ones. Then the electronic bill comes at the end of the month and you cannot remember what was purchased at each store. If you ordered an investigation from each store, they would be able to produce receipts showing exactly what you purchased. That would be your holiday artifacts. Just as receipts and stores can produce traces of everything you purchased during your shopping spree, digital forensics artifacts can provide traces of everything that happened on a computer during specified time periods.
File Signature – Technical:
Identification data that is contained in files to categorize the file type (Burgess Forensics, 2017). Signatures can also be determined by headers, the first few bytes within hexadecimal data (Bruno, n.d.).
File Signature – Nontechnical:
When you are working on documents and need to save them, you normally go to File, Save As, and choose a file type. After you save that file, it usually has an extension that identifies what kind of file it is, such as .doc for Word documents and .ppt for PowerPoint files. Those file types have assigned headers as well, so a forensics analyst can use hexadecimal data to determine file types even if a file extension has been modified or is not available. Those extensions and headers are file signatures, unique identifiers of the file types.
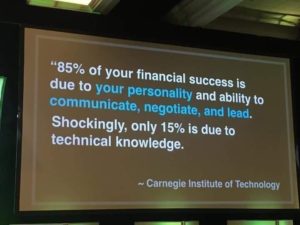
As security professionals, it is important to communicate based on appropriateness to the audience. In a court of law (staff meetings), we should assume that the listeners have no knowledge of the concepts and explain all terms in language that they can understand.
Read here for more tips about the importance of good communication skills.
References:
Bruno, G. (n.d.) Hex File Headers and Regex for Forensics Cheat Sheet v1.0. SANS Institute. Retrieved from: https://digital-forensics.sans.org/media/hex_file_and_regex_cheat_sheet.pdf
Computer Forensics Glossary (2017) Burgess Forensics. Retrieved from: http://burgessforensics.com/computer-forensics-glossary/
Mabuto, E., & Venter, H. (2013). SYSTEM-GENERATED DIGITAL FORENSIC EVIDENCE IN GRAPHIC DESIGN APPLICATIONS. Journal Of Digital Forensics, Security & Law, 8(3), 71-86.

